In a recent article published in Water Technology magazine, Indegy Director of Industrial Security and cyber-defense strategies guru, Chris Grove draws attention to the types of cybersecurity threats currently facing industrial water facilities. What he extols is rather surprising—while nuclear power plants sit on a fevered pitch against cybersecurity hackers, Mr. Grove says that for the water treatment industry, the most subversive threat lies in what he terms “insider threats”. The Trojan horse passing through the gates of Troy to applause and falling garlands, only by the glint of shadows does it spill its lethal payload of soldiers unto the slumbering streets.
Mr. Grove identifies three main tricks of Odysseus that typically prey on water facilities from the inside: the malicious insider, the compromised insider, and the negligent insider. The malicious insider mostly closely resembles Odysseus’s famous trick—these are the employees who’ve risen through the ranks and endeared themselves to a company before the empty their soldiers’ knives into operational technology that comprises the facility; they are the lease prevalent invasion. The compromised insider resembles the unaware leadership of Troy who welcomed the horse into their city as an offering. This type of threat entails an employee whose access to the facility’s networks has been hacked or pilfered by an external threat, which then, unbeknownst to the employee, uses their information to spindle into the network with malware and other harmful programs. Phishing scams that ask for user ID and passwords are the typical manifestations of this particular threat. Last and sadly most common of all, is the horribly-preventable negligent insider. This is plain and simple human error. Engineers, as every industry on earth knows, are perpetually overworked and under herculean mountains of stress—which can lead to miscalculations, overlooked procedures, and erroneous reporting. While this type of accidental threat is wholly preventable, to expect flawlessness under such scrutiny is incorrigible with human nature—a diamond after all, only achieves its perfection under immense and suffocating pressure. Negligent engineers are not carbon crystals waited to be spun immaculate. This would be the Trojan common sense—wholly negligent.
Mr. Grove’s conclusion is that the water treatment industry should employ the same measures it takes against cybersecurity to these insider threats.
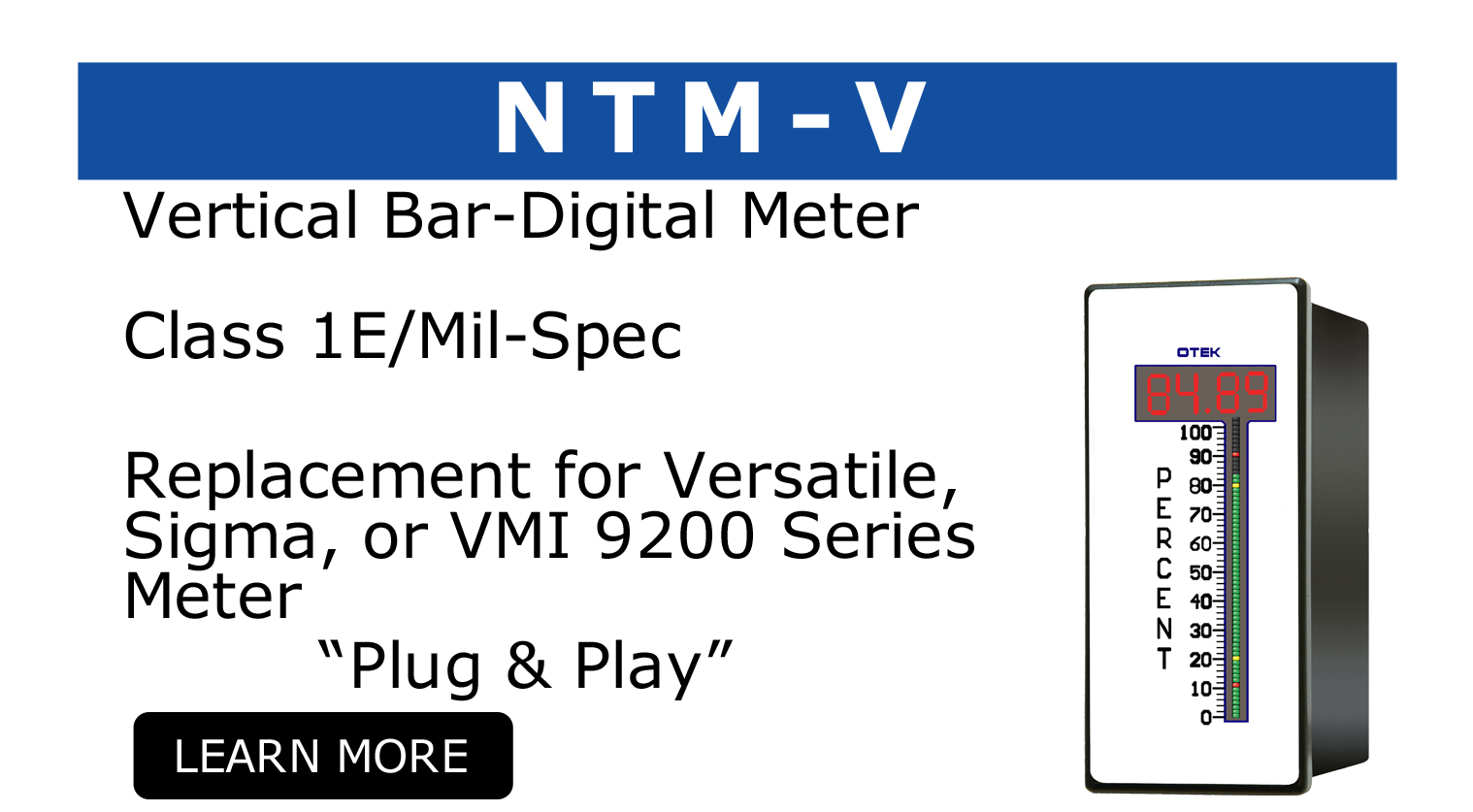
At OTEK we know a little bit about cybersecurity. Our Solid-State Analog Meter, colloquially referred to as the SSAM, was designed specifically to meet the cybersecurity regulation wrung around the nuclear industry by the NRC, in the form of NEI 08-09. When nuclear I&C rooms look to join the wave of digitalization they incur massive expenses in switching their analogs over to DAS systems that must pass ROI-bleeding security compliance measures. The SSAM avoids all that by being able to replace the obsolete ammeters individual using the wiring already in place and performing without any critical digital assets, rendering our new technology completely cybersecurity exempt.
For more information on OTEK and our products please call us at (520) 748-7900 or email our sales office at sales@otekcorp.com.
The full article in Water Technology magazine may be found here: https://www.watertechonline.com/cybersecurity-risks-industrial-water-fac…