As the manufacturing industry increasingly becomes more reliant on digital systems, they also become more vulnerable to cyber security attacks. Now it’s true that most U.S. manufacturers already have provisions or protocols for cyber security in place, but are they up to the ever-evolving tactics of cyber hackers? And if they plan to elicit government contracts, are they up to the Department of Defense’s (DOD) newly established standards?
In January of 2020 the DOD released the first of several versions of new security provisions, entitled the Cybersecurity Maturity Model Certification (CMMC)—essentially a vehicle for helping manufacturers to meet the requirements of NIST 800-171. Since NIST 800-171 was established in early 2018, manufacturing companies have mostly been allowed to self-monitor and regulate their own policies and provisions as they pertain to cyber security, provided, of course, they successfully meet the requirements of NIST 800-171. Under the newly implemented CMMC, manufacturers are now required to answer to third-party auditors to determine their level of competency in cyber security protection as mandated by NIST 800-171. Additionally, the auditor must give approval that the requirements are successfully being met prior to the award of the DOD contract, as opposed to the traditional after-the-fact inspection. And this, could be a problem, says solution consultant David Watts of information technology firm Avatara, ““If you don’t do this stuff, you’re nowhere near ready for CMMC. A lot of manufacturers are going to be caught flat-footed.”
Mr. Watts, in a recent interview with Modern Machine Shop, outlines five ways a company can improve its cyber security protection in consideration of CMMC:
- Training – Routinely providing knowledge and know-how to employees in charge of sensitive areas of company information, with updated protocols for phishing scams, emails asking for banking or password info, embedded ransomware, etc. Third-party auditors can then be shown when and how training sessions were conducted.
- Strengthened Passwords – CMMC requires level 3 standard passwords for DoD contracts. This includes characters, symbols, non-identical passwords, and limited log-in attempts
- Multi–Level Authentication – Beyond just a password, such as personal information/identification questions required to access servers.
- Continuous Monitoring – A program that checks all incoming and outgoing exchanges of information, looking specifically for indication of hacks such as malicious code, strange traffic patterns, etc.
- Real Life Protection – Storing sensitive information off-site, or cloud-based data storage is becoming more and more important. And while most companies won’t be employing armed guards to protect their servers, the easiest way in the world to steal information or plant malicious code is to insert a good ol’ USB drive.
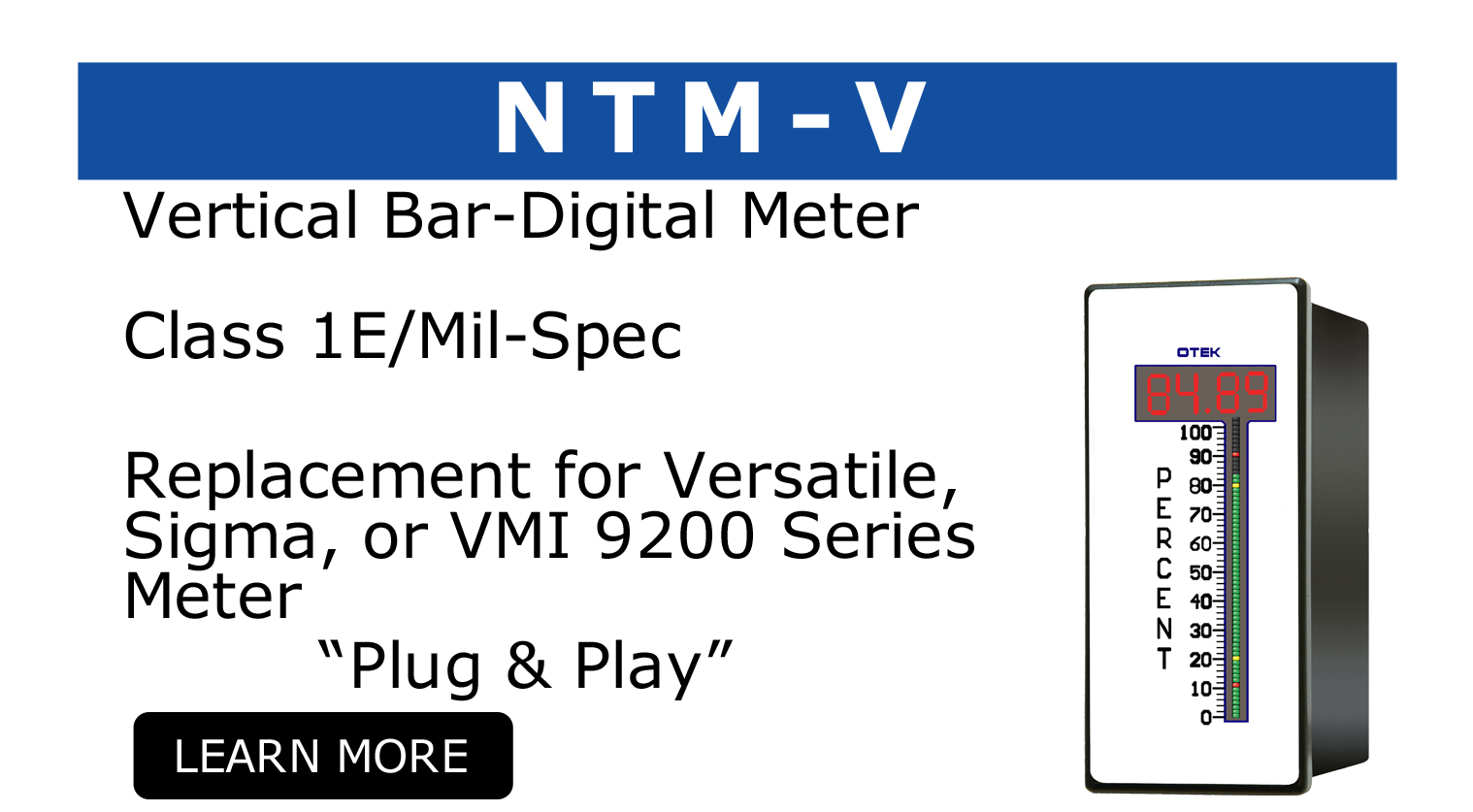
As a dedicated supplier to a host of industries, including the Nuclear and Military sectors, OTEK takes cyber security as seriously as we do the technology that powers our instruments. That’s why we created the industry’s first Solid-State Analog Meter, or SSAM—a digital instrument capable of harnessing the power that technology provides, while being comprised of analog hardware that renders it impervious to cyber security attacks.
For more information on the SSAM or OTEK’s cyber security measures, please call 520-748-7900 or emails sales@otekcorp.com