A malicious cybersecurity threat infiltrated one of India’s top nuclear power plants in recent days and leading security researchers have identified the Lazarus Group, a North Korean hacking team, as the culprit. Reports began surfacing Monday that the Kudankulam Nuclear Power Plant (KNPP) had been attacked by malware that resembled the notorious Dtrack trojan virus that has been in circulation recently—a form of malware that features keylogging, retrieving browser history, gathering IP addresses and information about connections, tracking running processes, and downloading all accessible files onto a disk or jump drives.
A former security analyst at India’s National Technical Research Organization, Pukhraj Singh, suggested in comments made public via Twitter that the malware was able to infiltrate the plant’s systems by surreptitiously piggy-backing off an internal anti-virus upload and then spreading outward from there. The evidence recovered included hardcoded credentials (which would have been used to bypass certain security measures) specific to the plant, indicating that the threat was designed to grow and multiply within the plant’s internal network. What’s perhaps more alarming is that sources claim the Indian government was made aware of a potential imminent attack back on September 4th, notified the KNPP itself, and yet the hackers were still able to get through.
Fortunately, the attack itself appeared to be only for reconnaissance purposes and was unable to reach the critical network controls that operate the plant’s nuclear reactors. That being said, the incorrigible fact that both the government and the plant itself had prior knowledge of a threat and it still was able to strike nearly unopposed is a disturbing glance at how vulnerable we truly are to this new era of cybersecurity criminality.
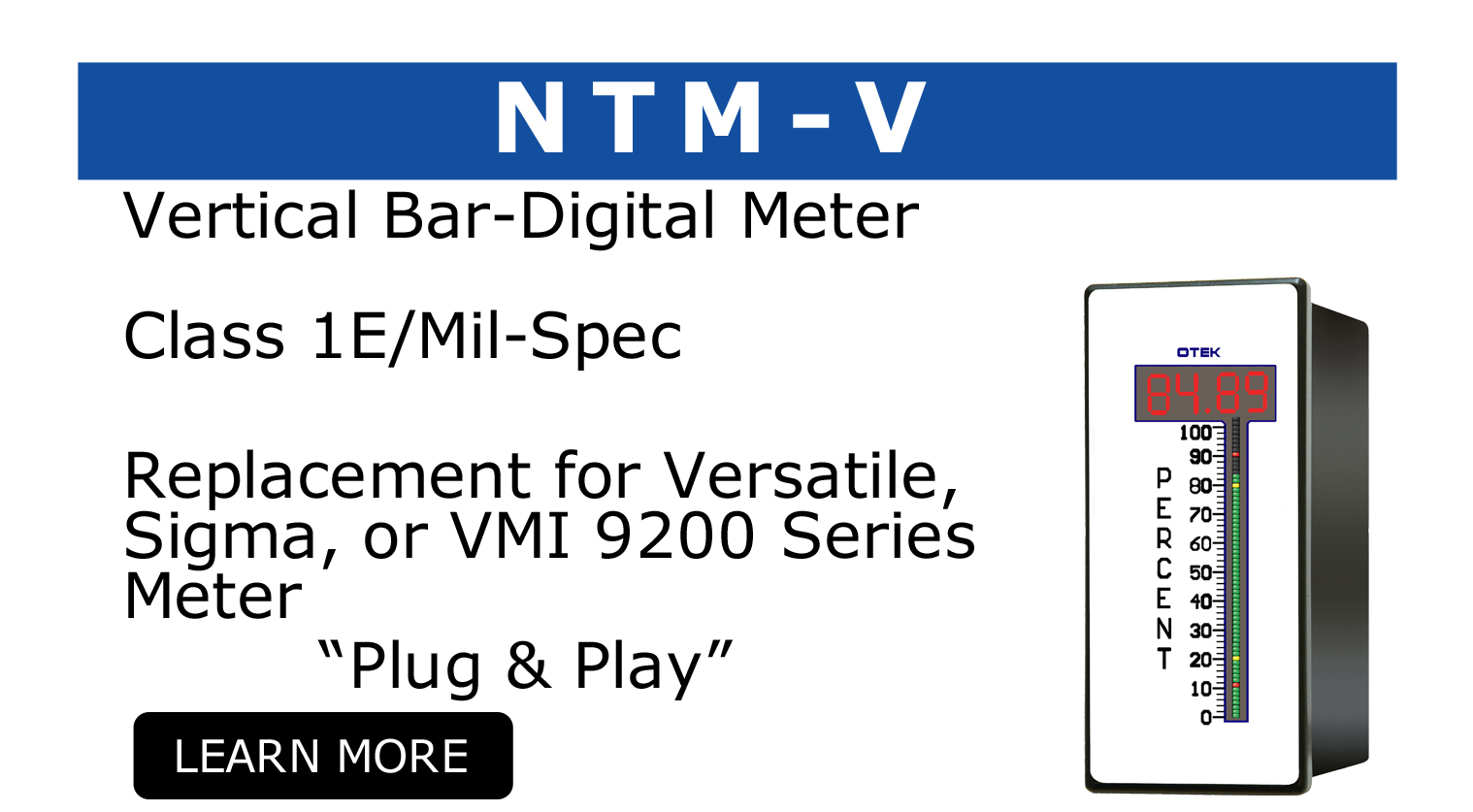
OTEK, in our enduring quest to aid the nuclear industry, has designed a new type of digital panel meter specifically designed to address cybersecurity concerns facing nuclear power plants around the world. The Solid State Analog Meter (SSAM) is a revolution within the industry as a fully functional ANSI 4” switchboard replacement for the popular DB40 and VS252 analog meters. Designed without any digital assets such as microprocessors, the SSAM classifies as Cyber Security Exempt under NEI 08-09 regulations.
Highlight features of the SSAM include:
- – Invulnerable to cybersecurity attacks due to the absence of non-digital components
- – Powered by the same award-winning OTEK technology that powers our NTM series
- – Advanced “pure white” LED technology allows for a powerful display that is customizable to a vast array of colors
- – Easily interchangeable scale plate designs without needing to remove the unit from the panel/wiring
- – Auto-Tricolor LED bar graph with 4 ½ digit display
- – Signal failure alarm alerts the operator in the event of loss of power or signal
- – The only analog portion is the input signal
In this new digital world where criminals lurk with unseen fingers upon keyboards anywhere in the world, we must do better to be vigilant in how we protect and defend critical institutions such as nuclear power plants. The SSAM is OTEK’s contribution to that fight.
For more information on the SSAM or any of our other products, please call 520-748-7900 or email our sales department at sales@otekcorp.com.